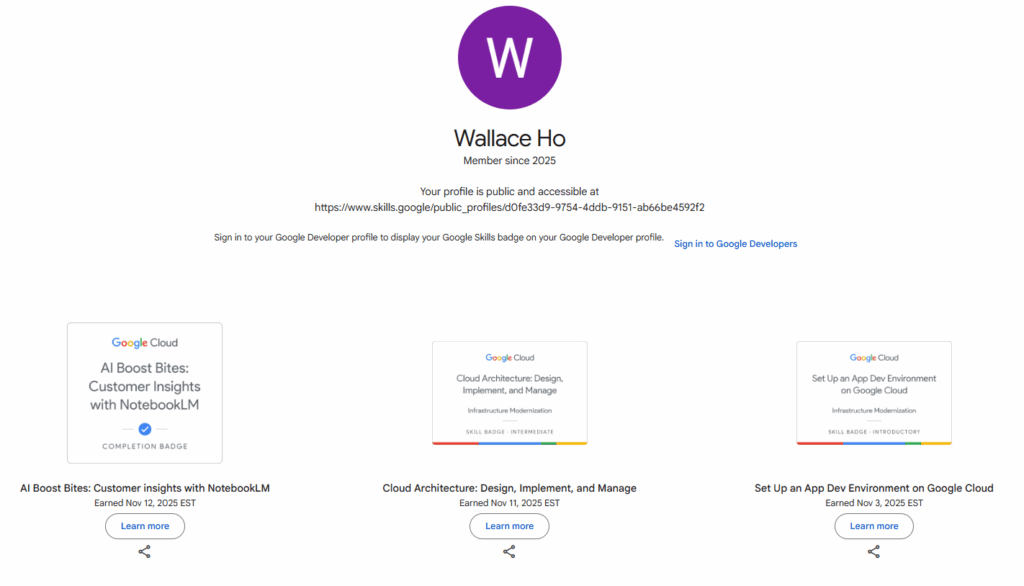
The next chapter.. Google Cloud

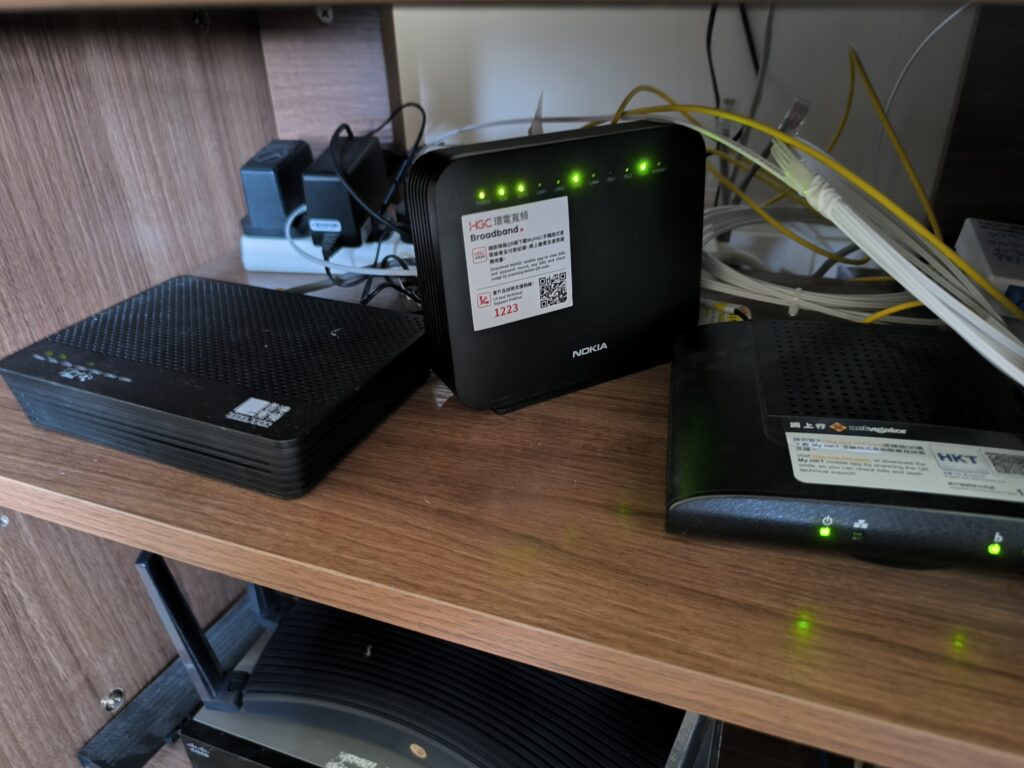
It was planned for a while, just have chance to upgrade the home router to support dual WAN with 2.5Gbps ports. I have then applied another provider for broadband service with at least 1Gbps bandwidth.
Cabling is a pretty hard work, the pipe is tiny and need to fit in a lot of fiber and CAT5 cables. Luckily the GPON spitter is just one floor below.

Alright, installation completed, now there are 3 ONT from 3 service provider (HKT, HKBN and HGC) placed at the same location. It proivdes up to 3Gbps bandwidth to my home.
Dual WAN connected with load balancing mode (P.S: Not a link aggregation)
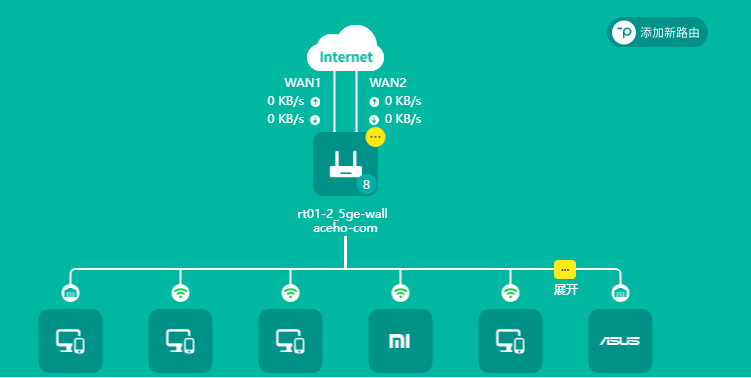
Finally, speed testing! Unfortunately, I yet not have a 2.5Gbps network card but I got a mobile support Wi-Fi 6 (802.11ax) with 160Mhz which can theologically support up to 2401Mbps. With dual WAN connection, the download speed can boost up to around 1550 – 1800 Mbps.

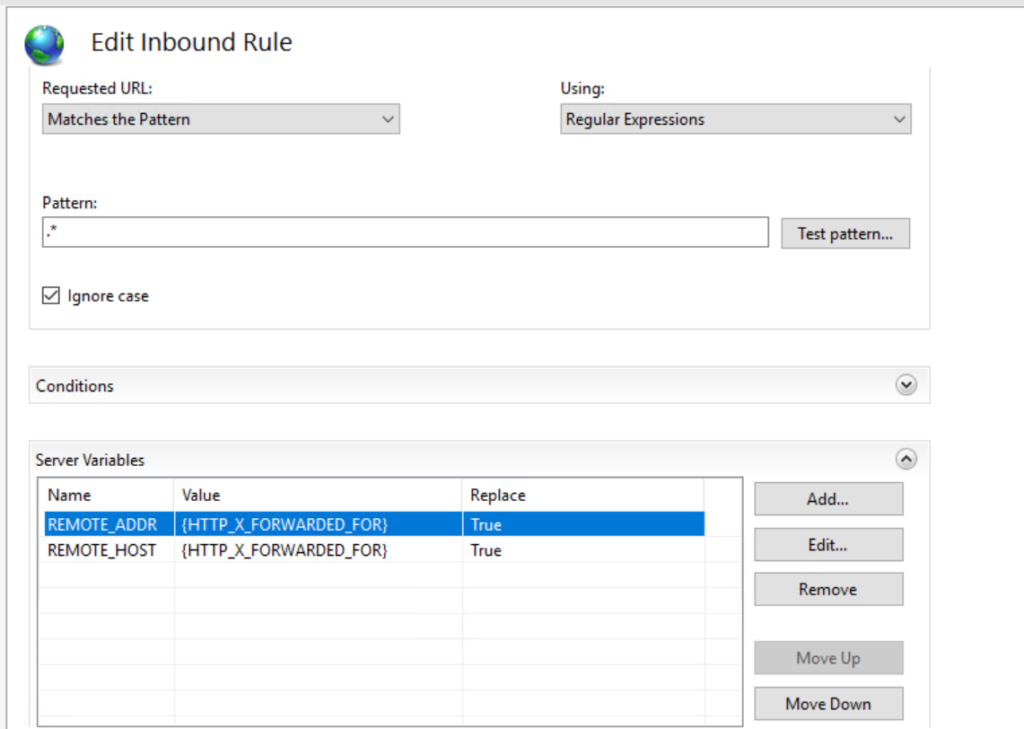
Sometimes, you may need to use URL rewrite to overwrite the HTTP header. For example, if you are using Cloudflare or any CDN, the REMOTE_ADDR and REMOTE_HOST will be appeard as internal IP of the CDN provider.
If you are using IIS, there is no option to do URL rewrite by default. You will need to download and install an app call “URL Rewrite” and then you will get an option to edit the rule.
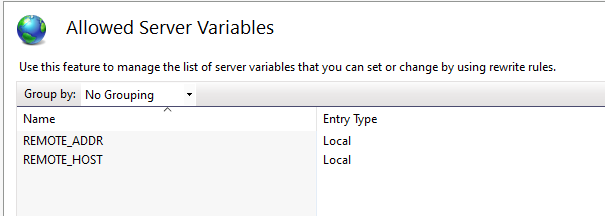
The tool can be downloaded from https://www.iis.net/downloads/microsoft/url-rewrite